📂 Enumeration
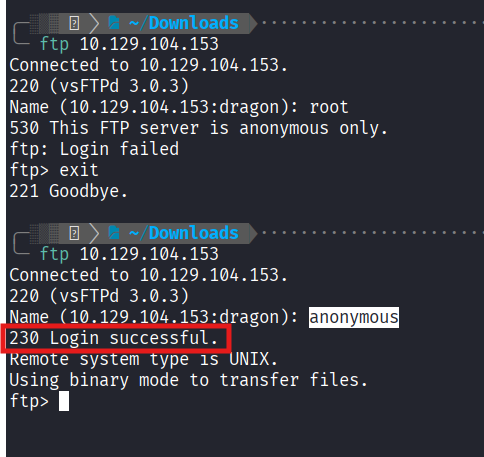
1. FTP Enumeration / Exfiltration
Logging into the FTP server anonymously to retrieve the mentioned lists.
Steps:
- Connected via
ftp 10.129.104.153. - Logged in as
anonymouswith no password. - Downloaded the following files:
allowed.userlistallowed.userlist.passwd
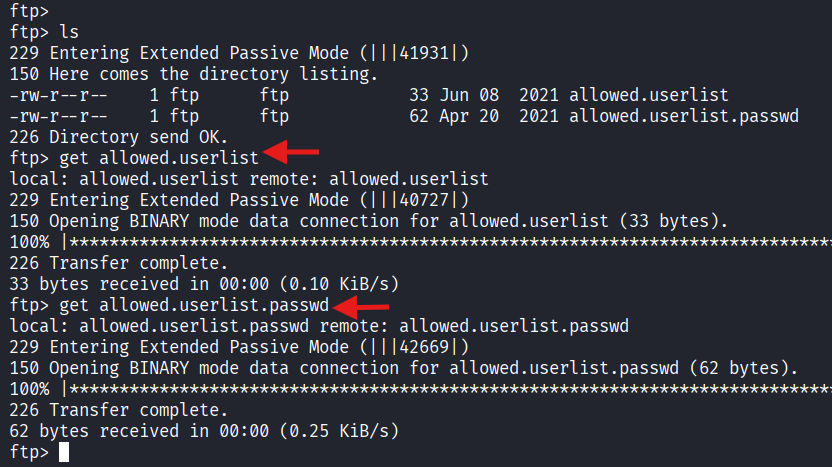
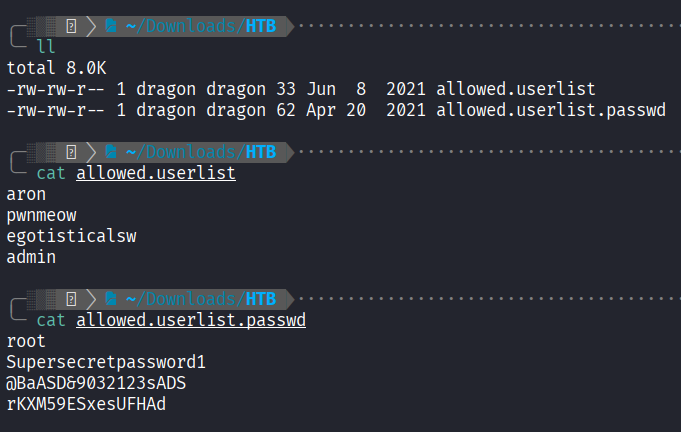
2. Credential Analysis
Inspecting the exfiltrated files:
- Users:
aron,pwnmeow,egotisticalsw,admin - Passwords:
root,Supersecretpassword1,@BaASD&9032123sADS,rKXM59ESxesUFHAd
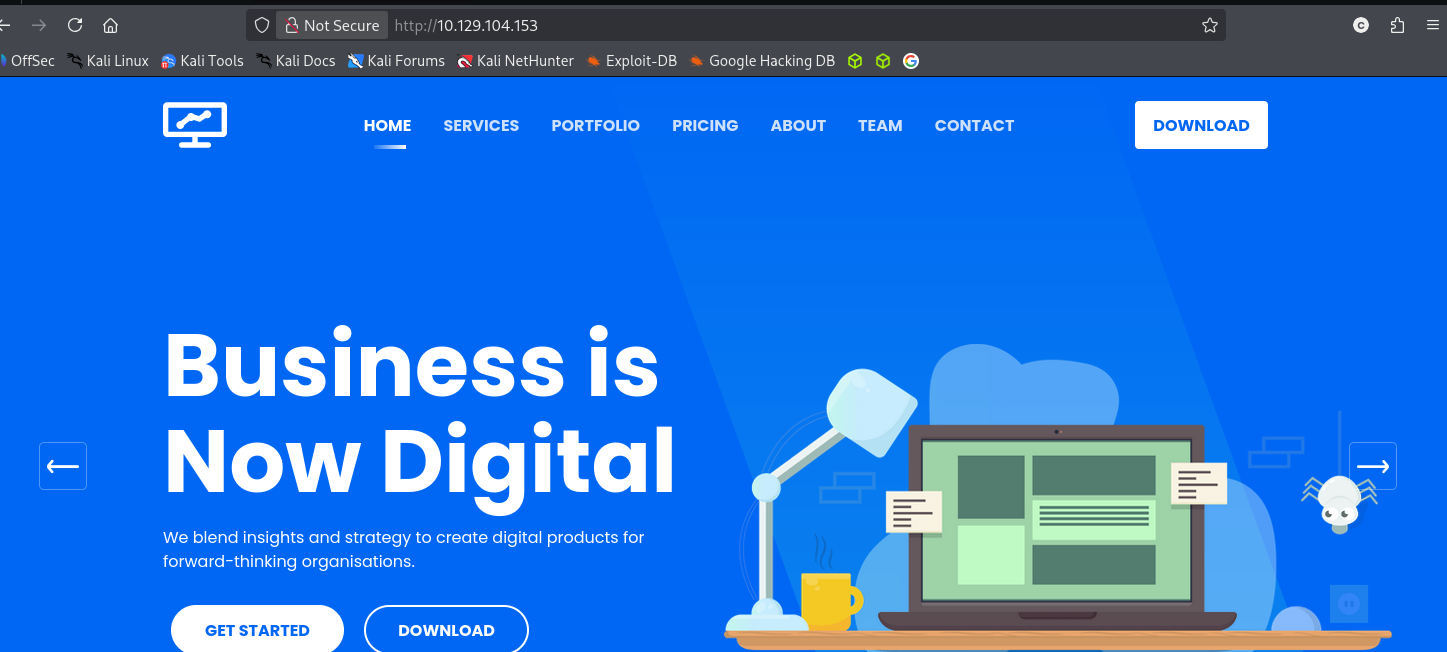
3. Web Service Enumeration
Navigating to http://10.129.104.153 reveals a business template landing page with no obvious login fields.
Directory Bursting
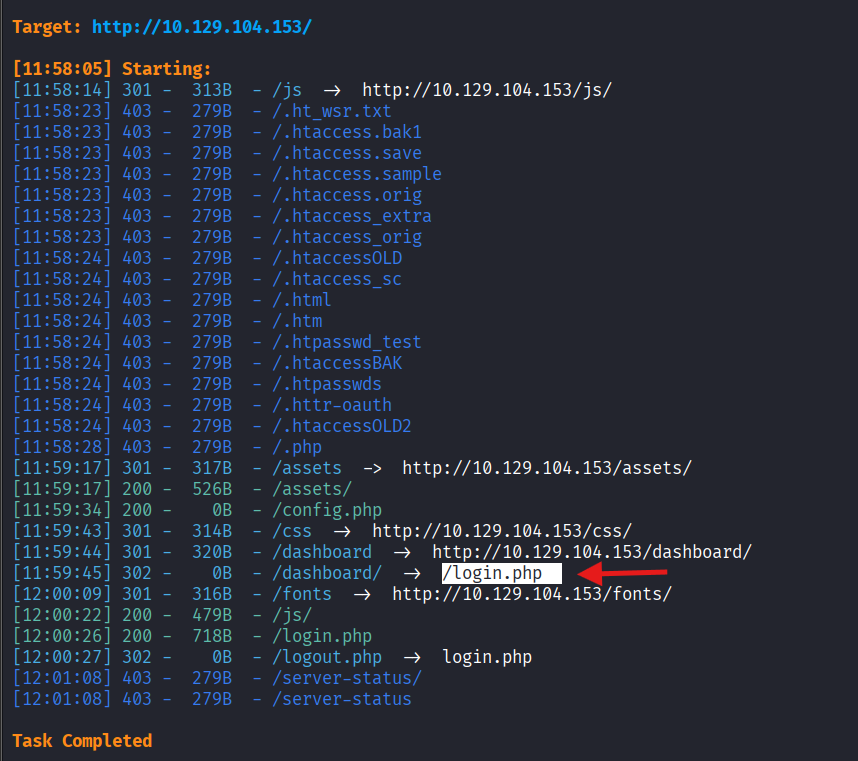
I used dirsearch to find hidden directories and files.
Command:
dirsearch -u http://10.129.104.153/Results:
Discovered /login.php and /dashboard/.
Next Step